
Introduction to Threat Modeling
January 3, 2022
Topics
- Cybersecurity

January 3, 2022
Topics
Threat modeling is a structured approach of identifying and prioritizing potential threats to a system and determining the value that potential mitigations would have in reducing or neutralizing those threats. Threat modeling is needed because of the dynamic nature of security. In this post we’re going to talk about the steps your organization can take to identify any possible threats and vulnerabilities that are currently present or might arise in the future and take a proactive approach to mitigate them.
The first step an organization should take is to map out their entire infrastructure. This should not only include all devices and endpoints but should also cover physical locations, third party services, and pretty much anything that could be used as an attack vector to gain access to your organization.
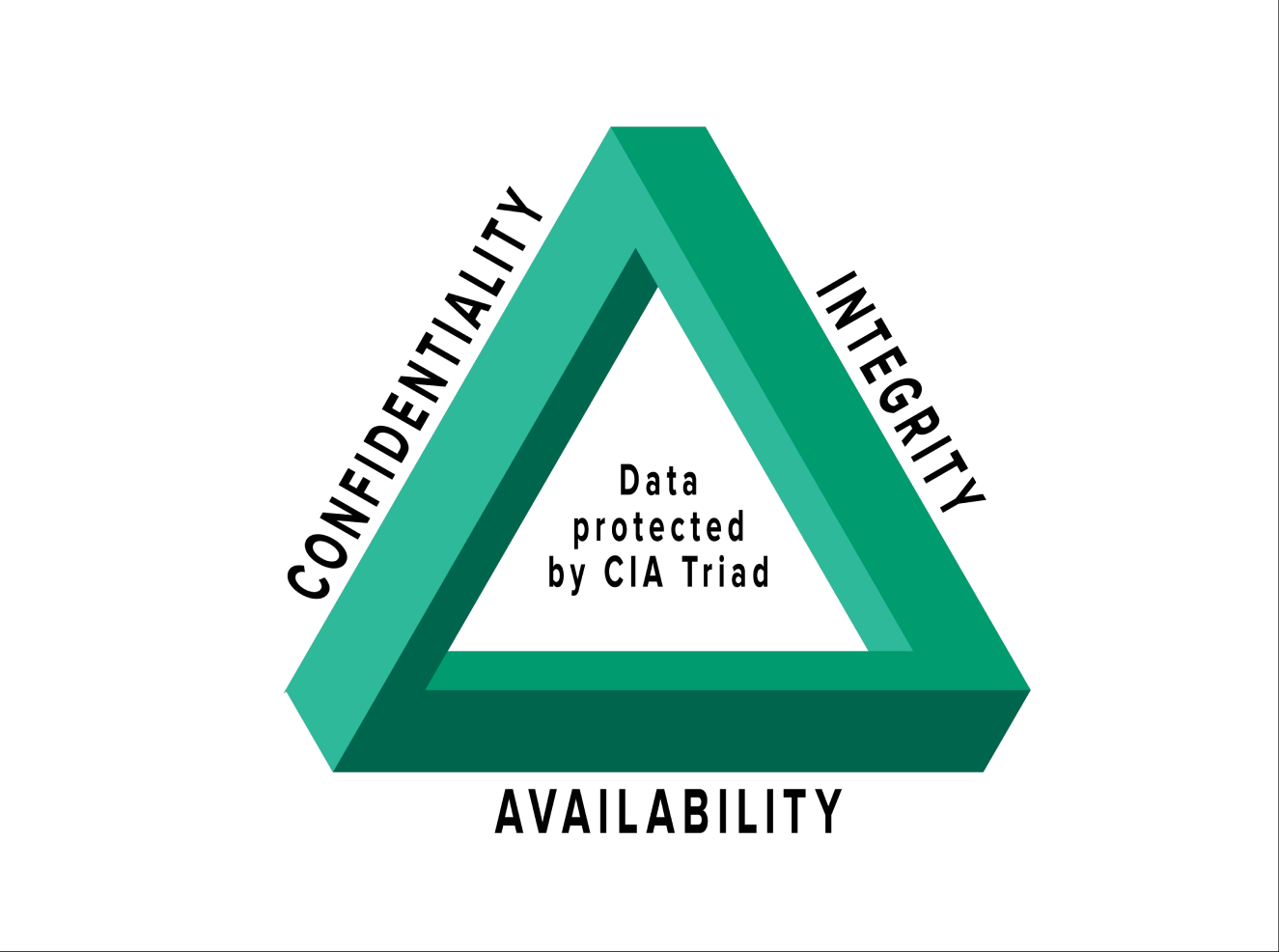
Once this is done, your organization should go through each part and ask, “If this were to fail, does this affect any principles defined by the CIA Triad?” In the information security community, “CIA” has nothing to do with a certain well-recognized US intelligence agency. These three letters stand for confidentiality, integrity, and availability. Together, these three principles form the base of any organization’s security infrastructure. In fact, they should function as goals and objectives for every security program. The CIA triad is so foundational to information security that anytime data is leaked, a system suffers a DDoS attack, a website is taken down, or any other security incidents occur, you can be certain that one or more of these principles has been violated.
Next, we need to ask, “What types of threats is our organization vulnerable to?” These can be broken down into four categories:
• Adversarial – Consists of every type of hacker from the script kiddies to nation state actors.
• Accidental – Covers employees accidentally unplugging hardware or pushing buggy code to a production environment.
• Structural – Includes the physical infrastructure of your organization’s environment.
• Environmental – Deals with natural disasters such as earthquakes or severe weather.
Once your organization has a good understanding of the type of threats your infrastructure is exposed to the next step is to work with the IT and security teams to find the best solution to securing it. At this point your organization must find the balance between securing everything like its Fort Knox, budget concerns, and the availability of data to users in your organization, among other things.
Ideally this process should be done as often as possible because threats are constantly evolving and changing but it is up to your organization on what they see fit. Realistically it should be done any time there is a major infrastructure change or any new products or services are added to your environment.
The attack and defense sides of security are constantly changing. As part of handling this change, organizations should continually reassess and evolve their defenses. This includes adopting continuous monitoring practices, security automation technologies, and threat intelligence feeds to detect new vulnerabilities and attacks in near real-time. This proactive approach is the best way to protect your organization against threats.